Why we give so much to CSAW
In just a couple of weeks, tens of thousands of students and professionals from all over the world will tune in to cheer on their favorite teams in six competitions. If you’ve been following our blog for some time, you’ll know just what we’re referring to: Cyber Security Awareness Week (CSAW), the nation’s largest student-run cyber security event. Regardless of how busy we get, we always make time to contribute to the event’s success.
CSAW holds a special place in our hearts.
We are proud of our roots in academia and research, and we believe it’s important to promote cyber security education for all students. We’ve been involved in CSAW since its inception. Dan and Yan competed as students, and went on to play a central role in the early years. Since then, our employees have contributed to events, particularly CTF challenges; our favorite flavor of CSAW. (Special kudos to Ryan and Sophia for all the time and effort they’ve contributed). In fact, several of our staff competed as students before joining our team. Here’s looking at you, Sophia and Sam. Finally, we feel fortunate to have met our most recent intern, Loren, through the affiliated CSAW Summer Program for Women.
Part of what makes the CTF so great is that it incorporates diverse contributions by an array of collaborators. The resulting depth of expertise is hard to match.
This year, we contributed five CTF challenges for the qualifying round
wyvern
Participants start with an obfuscated Linux binary asking for input when run (aka a crackme). Heavy obfuscation, using varying degrees of false predicate insertion, code diffusion, and basic block splitting (all possible through LLVM) would make this a leviathan of a static-reversing challenge. Instead, participants had to pursue a dynamic approach, and program analysis tools to brute force the flag. In the process, they learn how to leak which path the program takes by monitoring changes in instruction counts, and how to use tools such as PIN, Angr, or AFL.
bricks of gold
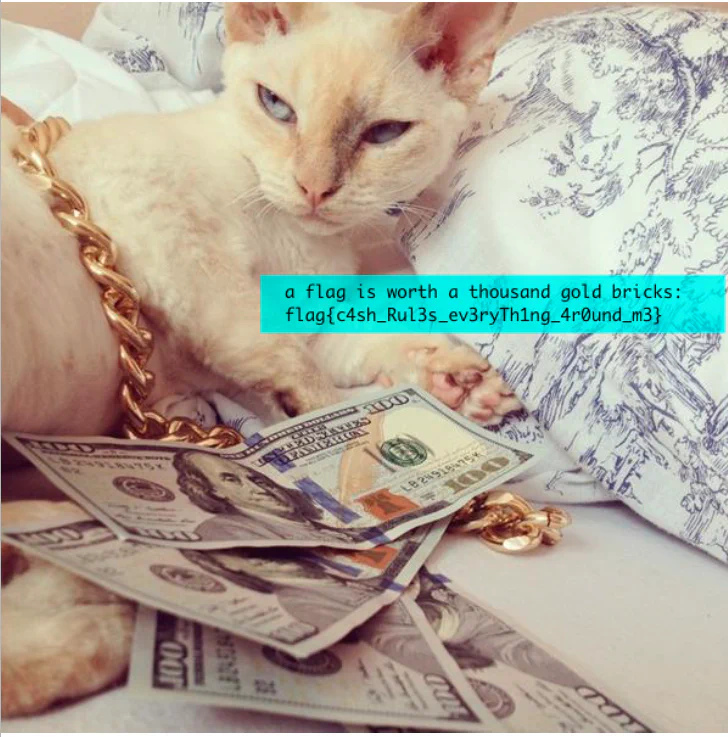 This challenge began with a note of international mystery: “We’ve captured an encrypted file being smuggled into the country. All we know is that they rolled their own custom CBC mode algorithm – it’s probably terrible.” Participants must successfully decrypt the file’s custom XOR-CBC encryption. That lead them to seek the algorithm, the key and the IV. Doing so required knowledge of file headers, cryptography, and brute force. Participants also learn how to examine an encrypted file for low entropy, unencrypted strings, and CBC mode block patterns.
This challenge began with a note of international mystery: “We’ve captured an encrypted file being smuggled into the country. All we know is that they rolled their own custom CBC mode algorithm – it’s probably terrible.” Participants must successfully decrypt the file’s custom XOR-CBC encryption. That lead them to seek the algorithm, the key and the IV. Doing so required knowledge of file headers, cryptography, and brute force. Participants also learn how to examine an encrypted file for low entropy, unencrypted strings, and CBC mode block patterns.
sharpturn
Participants receive an archive of a broken git repository. They need to fix the corruption and read the files. In fact, there are three corruptions: each one is a single bit off and are all contained in individual source code files. (This actually happened to Trail of Bits.) Once repaired, the source code files compile into a binary with the answer embedded inside. Participants learn how Git blobs contain versions of repository files that have been prepended with a header and zlib compressed. Git’s versioning provides enough information to rebuild the broken commits. They must dig into the lower-level details of how Git is implemented to write a recovery program.
punchout
The story opens with three binary blobs taken from IBM System/360 punch cards, and their encrypted data. These cards were encrypted with technology and techniques from 1965, requiring participants to research how security worked in that era. They also encounter ciphers like KW-26, which generated long streams of bits and XOR’d them against the plaintext, and IBM’s use of ebcdic -not ascii- for encoding. The same stream of bits was used to encrypt each blob, and this cryptographic key reuse has a known attack. Participants attack the cipher with “cribs” in a process known as “crib dragging.”
“math aside, we’re all blackhats now”
Participants must identify the security industry consultant working for the TV show ‘Silicon Valley.’ During its first two seasons, discerning viewers noticed all kinds of props, name dropping, and references to the CTF community, with notable accuracy in its security-related plot elements. There is no way the show’s producers could have learned all these references on their own. Someone had be to feeding them inside information. Who could it be?
1,367 teams scored at least one point, which already makes the event a resounding success in our books. We’re looking forward to watching the CTF finalists duke it out in New York. If you missed the deadlines, you can always find our old CTF challenges on Github.
T-shirt bounty for writeups
For a few bribable teams willing to s
 hare their thought processes, we’re passing out these snazzy t-shirts for posting helpful writeups. We think it’s pretty cool to send these shirts all over the world, including England, Canada, Australia, and Singapore!
hare their thought processes, we’re passing out these snazzy t-shirts for posting helpful writeups. We think it’s pretty cool to send these shirts all over the world, including England, Canada, Australia, and Singapore!
Thanks and kudos to:
| bricks of gold negasora team ascii_overflow | wyvern yrp604 | sharpturn nandy narwhals team K17 thehobn Lense randomProgrammer |
|---|
Shaped the Policy competition
Wassenaar shone a spotlight on an array of issues we’ve been tackling for years now. We’re big supporters of the Coalition for Responsible Cybersecurity’s mission to ensure that U.S. export control regulations don’t negatively impact U.S. cybersecurity effectiveness.
So, it seemed only natural that we’d assist CSAW with its policy competition. We love the idea of the US Government hosting a bug bounty. We, as a country, could buy a lot of bugs for the billions wasted on junk security. Our topic challenged students to explore this idea and present a workable solution. We were delighted to see an exploration of this topic in the Army’s Cyber Defense Review recently.
Submissions were judged by a panel of experts in the field representing all sides of this contentious question. The top five teams will present their proposals in-person at CSAW. The top three teams will receive cash prizes and some serious attention from industry experts.
No more THREADS
After three years of running THREADS, we’ve decided to refocus our contribution to CSAW on the competitions. We hope you’ll join us in helping motivate and educate students of every academic level. (If you’re out of your school years and in New York, you might be interested in coming to our Empire Hacking meetup.)
May the best teams win.
