Enabling Two-Factor Authentication (2FA) for Apple ID and DropBox
In light of the recent compromises, you’re probably wondering what could have been done to prevent such attacks. According to some unverified articles it would appear that flaws in Apple’s services allowed an attacker to brute force passwords without any rate limiting or account lockout. While its not publicly known if the attacks were accomplished via brute force password guessing, there has been a lot of talk about enabling Two-Factor Authentication (2FA) across services that offer it. The two most popular services being discussed are iCloud and DropBox. While setting up 2FA on these services is not as easy as it should be, this guide will step you through enabling 2FA on Google, Apple ID and DropBox accounts. It’s a free way of adding an extra layer of security on top of these services which handle potentially sensitive information.
What is Two-Factor Authentication?
Username and password authentication uses a single factor to verify identity: something the user knows. Two-Factor authentication adds an extra layer of security on top of a username and password. Normally, the second factor is something only the real user has. This is typically a temporary passcode generated by a piece of hardware such as an RSA token, a passcode sent as an SMS to the user’s cell phone, or a mobile application that accomplishes the same function.
With two-factor authentication, stealing a username and password won’t be enough to log in — the second factor is also required. This multi-factor authentication means an attacker will be required to compromise a user above and beyond password guessing or stealing a credentials database. An attacker would have to gain access to the source of the extra, unique and usually temporary information that makes up the 2FA.
Most services provide 2FA tokens through multiple means (SMS, mobile application or separate hardware token), however setting up 2FA on these services can sometimes be tricky. 2FA is still not enabled by default and users are not forced to use it.
An explanatory video from Google about their version of 2FA (you should use this too)
Use a unique password for all of your accounts on top of 2FA. Attackers may have access to lists of passwords and usernames from other websites that have been compromised. These lists may contain your username and password as well. With 2FA enabled, they’ll be missing that last piece of the puzzle for account authentication.
Apple ID
Apple allows you to setup both an SMS and Mobile Push 2FA. Mobile Push means the 2FA code will be delivered to your phone using Apple’s Push messaging system.
While Apple has implemented 2FA for some services it has not been rolled out completely, most notably iCloud. Apple has been seen testing 2FA on iCloud but has not launched support yet. Once Apple rolls out 2FA support for iCloud you’ll most likely be prompted for the 2FA code automatically. There should be no enrollment process for iCloud separate from the rest of the Apple 2FA enrollment process below.
For the purposes of this tutorial, we’ll be setting up SMS only, as that will be the most compatible and cover 2FA setup process for all phones, not just iPhones.
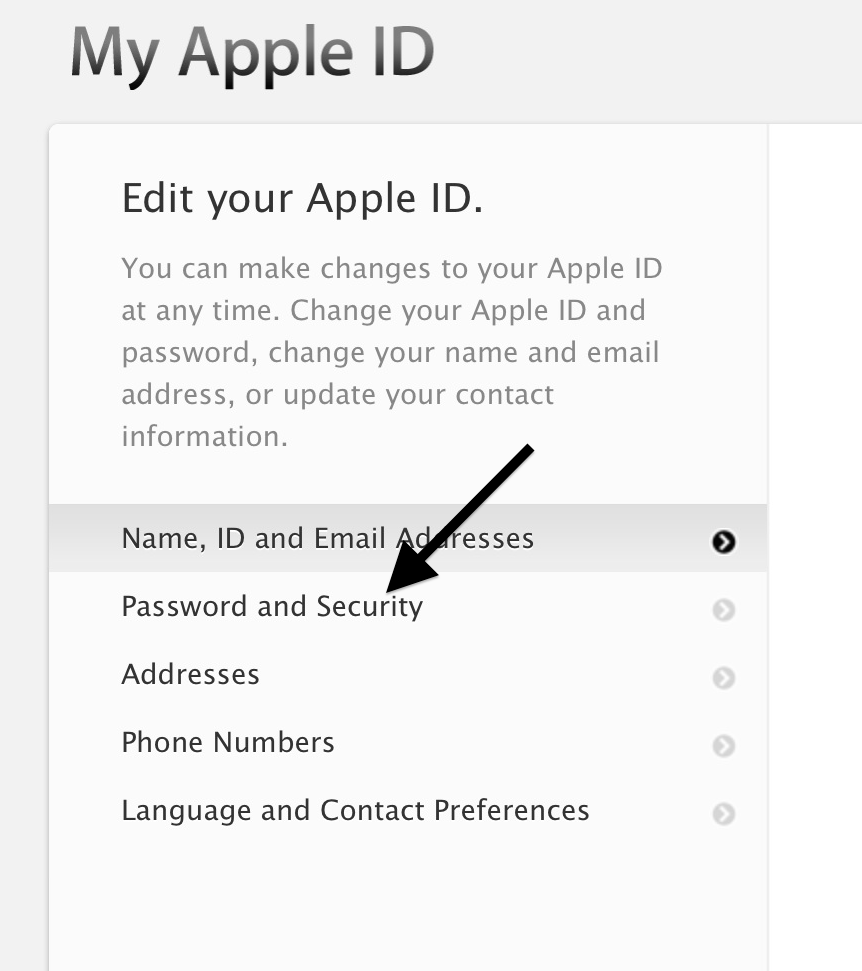
1. Sign into your Apple ID at https://appleid.apple.com and click “Password and Security” from the menu on the right:
You will be asked to answer your personal security questions to proceed.
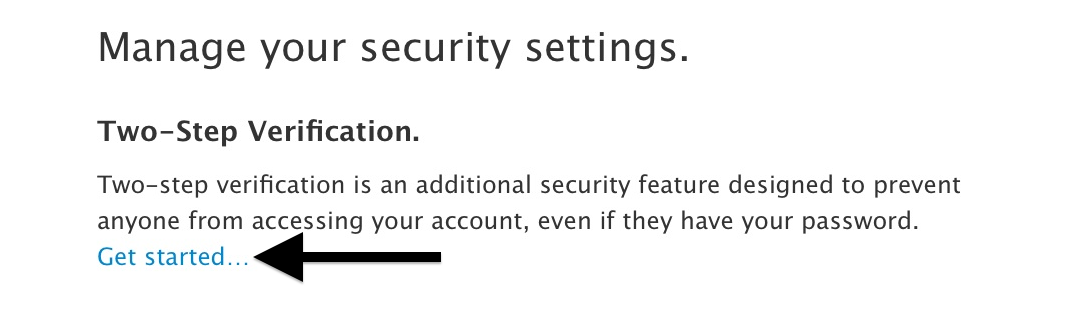
2. At the very top you’ll see a paragraph explaining Two-Step Verification. Click “Get Started” to enroll.
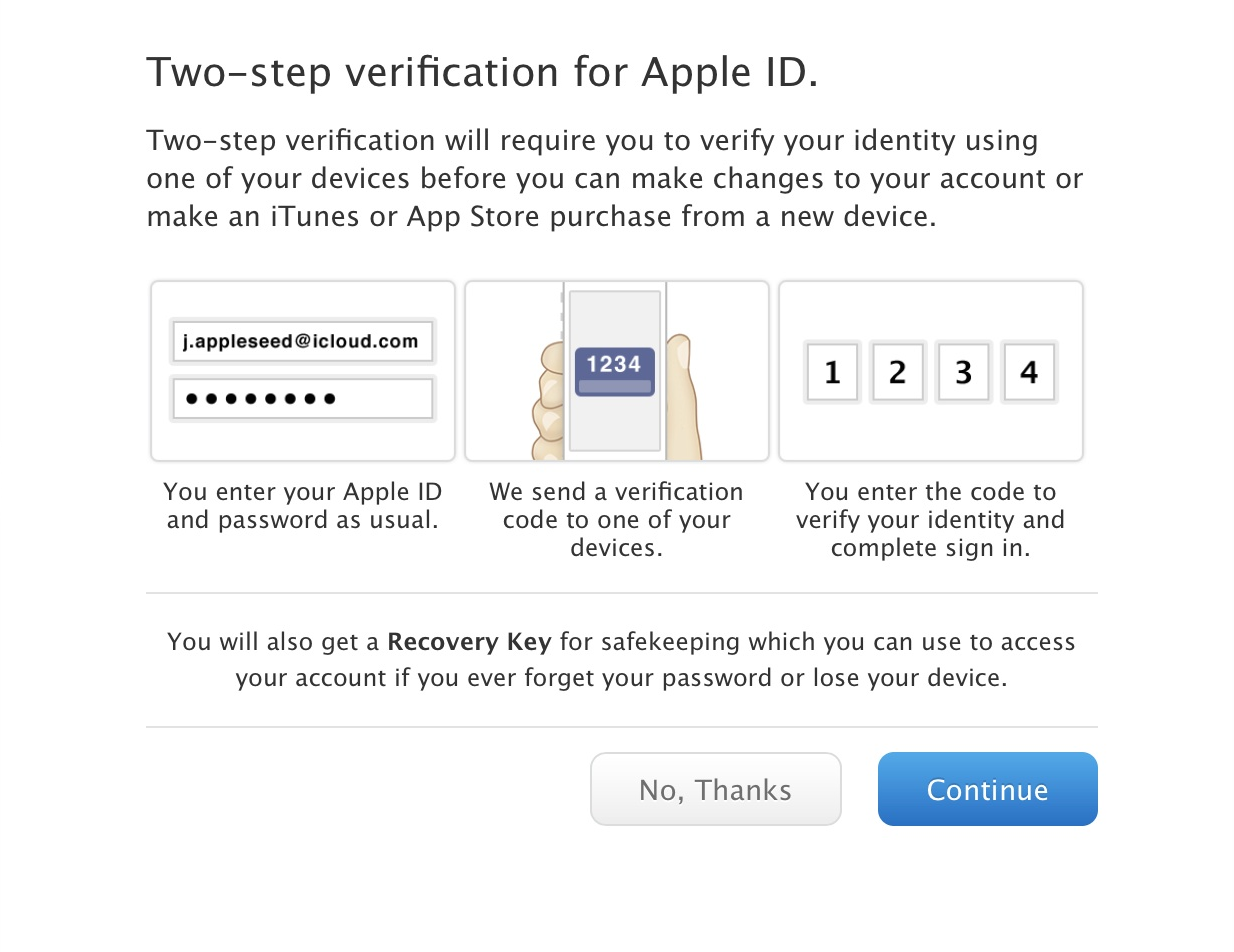
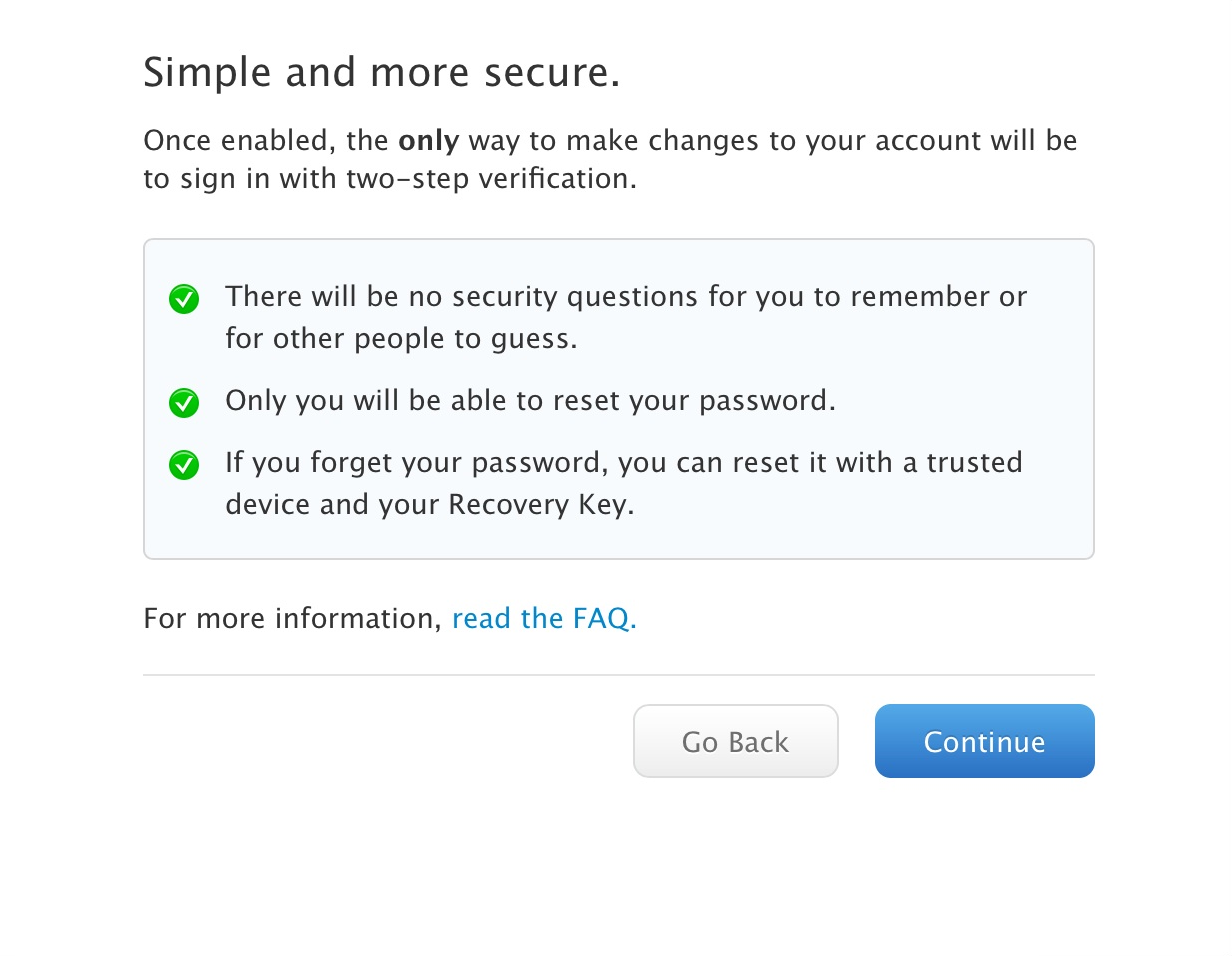
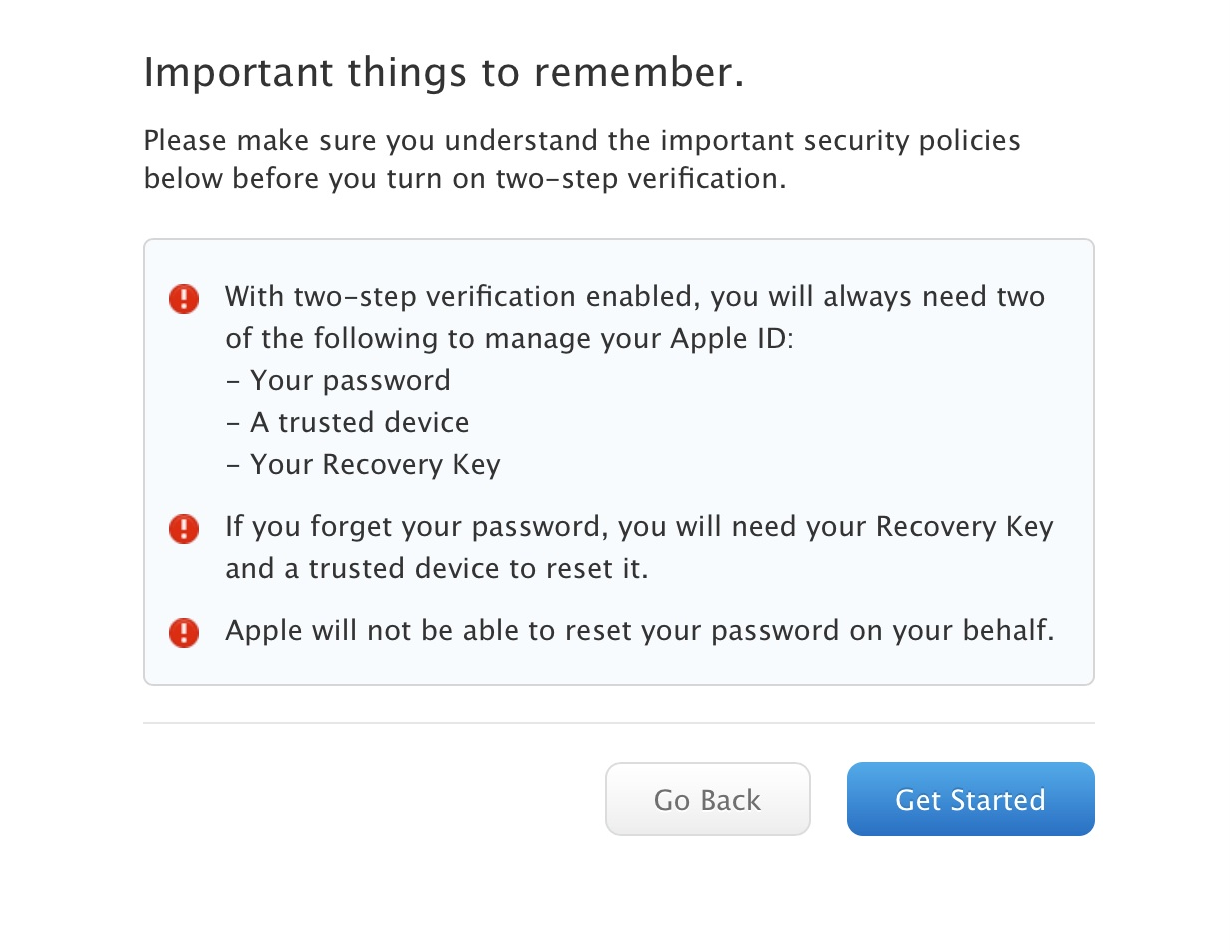
3. Apple will ask you to read a few notices before you begin Step 1 of the enrollment process. Read each screen and click continue until you get to the first step. Each screen is shown below:
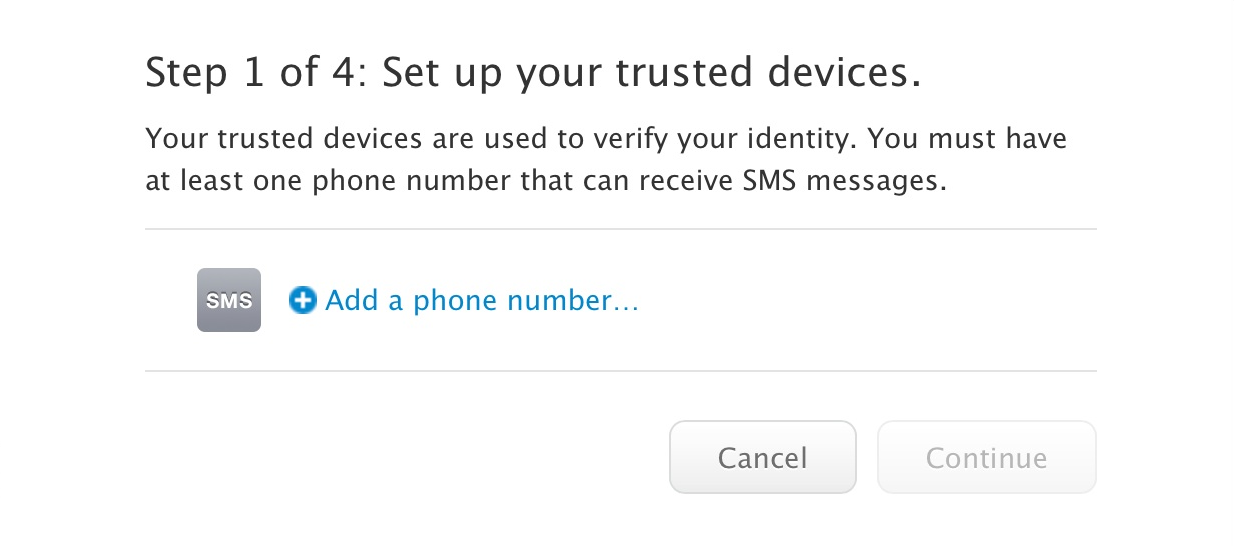
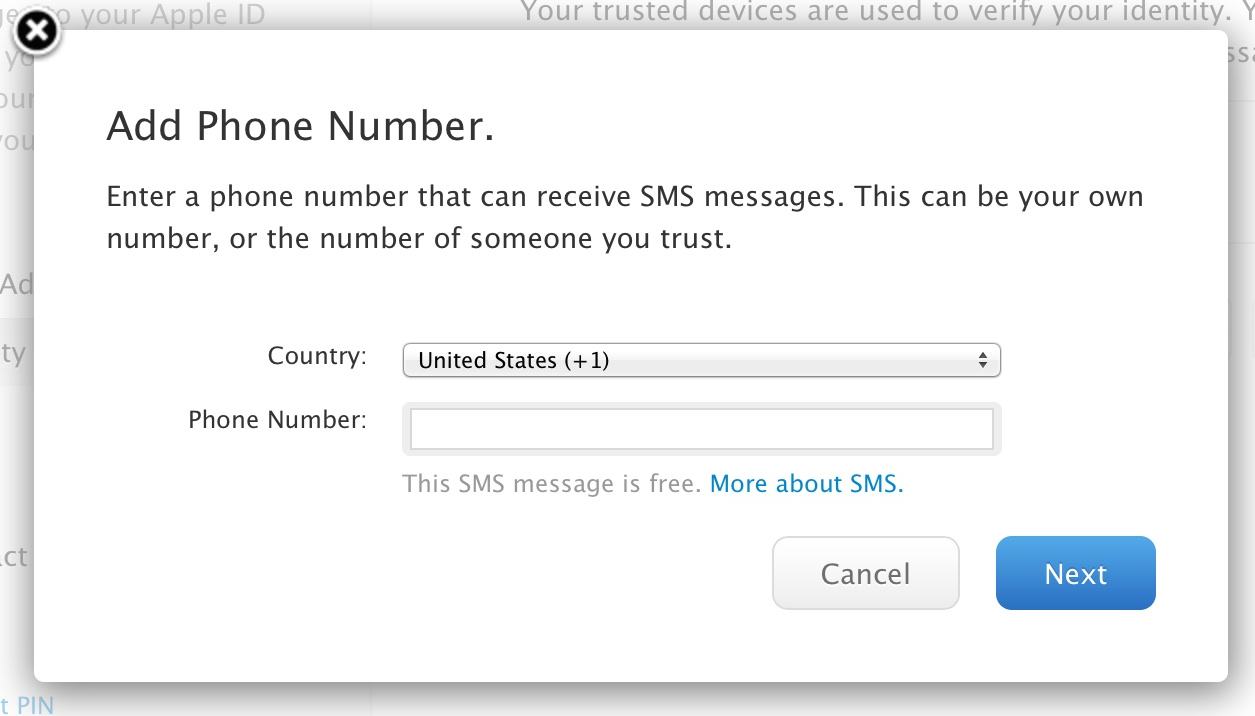
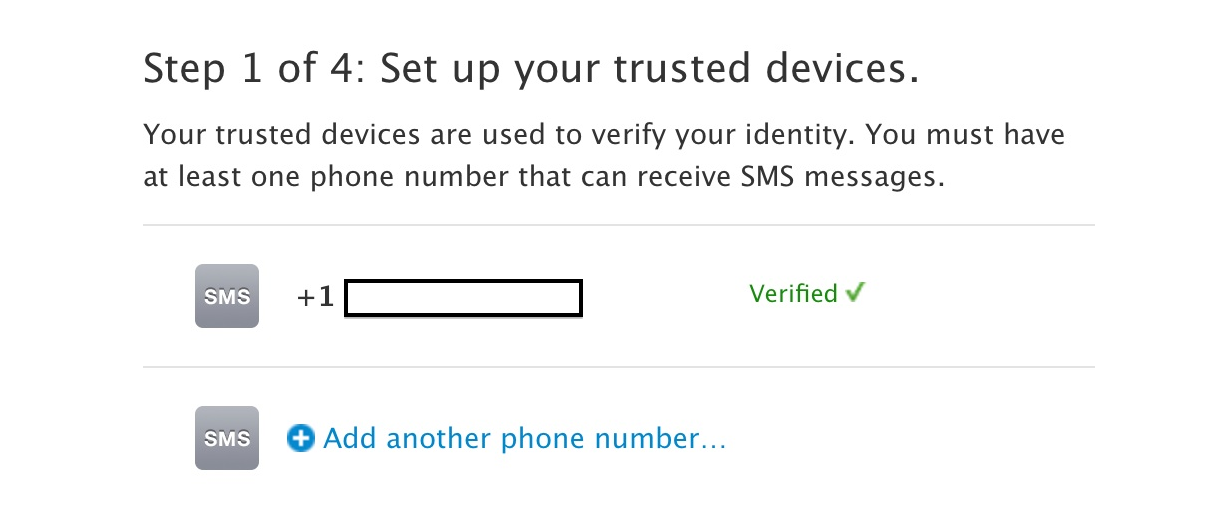
4. Apple will now ask you to provide your mobile phone number. This will be used to send you a Two-Factor Authentication token as an SMS to verify the phone number you entered is yours and in your physical possession.
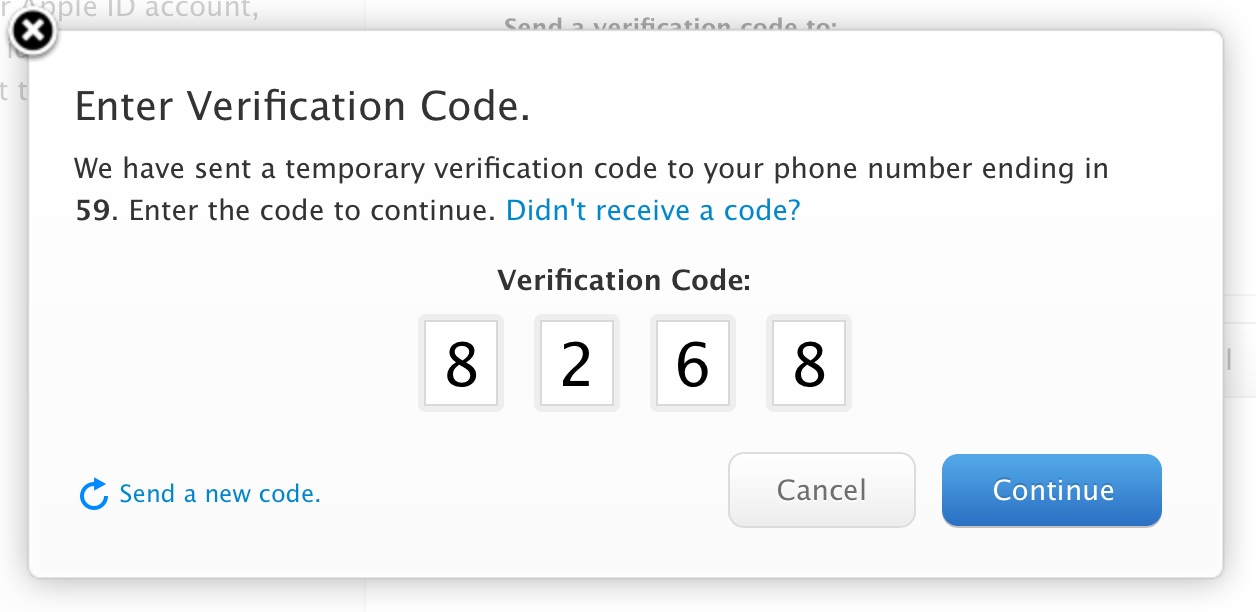
After entering your cell phone number, an SMS will arrive with a 4 digit code.
The Apple website will ask you to enter this code.
Once you’ve entered it your phone number will be “verified”.
Press “Continue” to proceed.
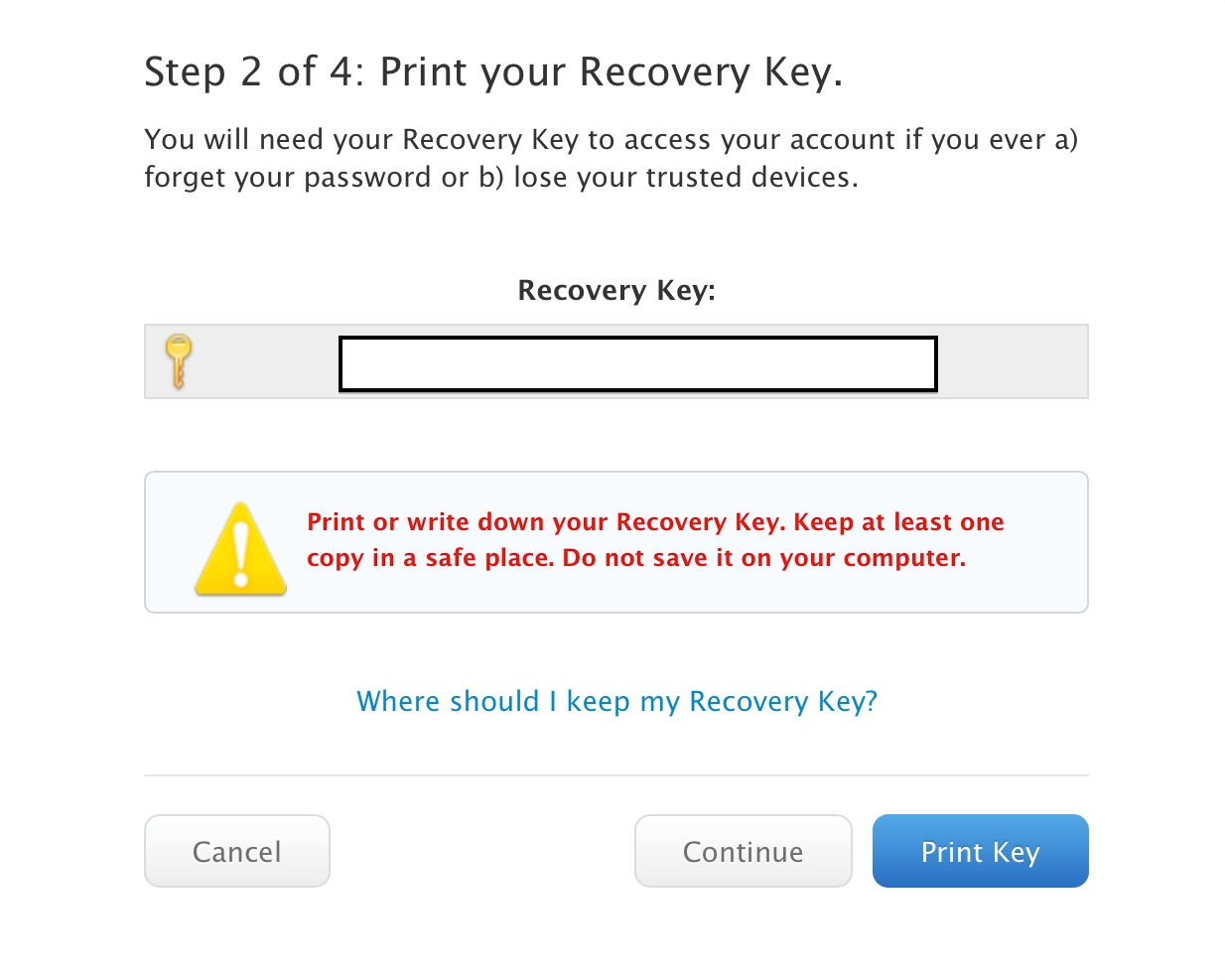
5. Apple will now provide you with a “Recovery Key” in case you lose possession of your phone or phone number. This is a secret code that will allow you to recover your account in the event something goes wrong with your Two-Factor Authentication procedure. It is very important you keep this code secure and private! With this code, an attacker may be able to compromise your account. Don’t store this code electronically on your computer. Print it and put it in a safe place.
Without it, you could become locked out of your Apple account without any recourse.
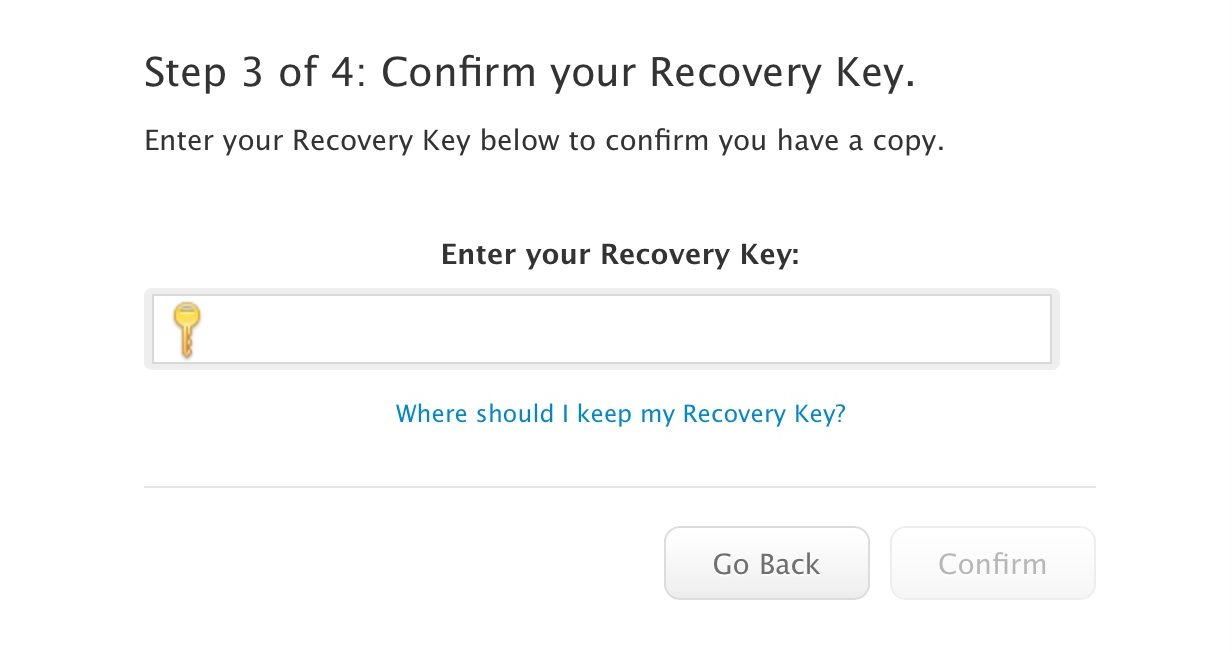
6. Apple will now ask you to re-enter your “Recovery Key”. This ensures that you have copied it down and it is now your responsibility to store it securely.
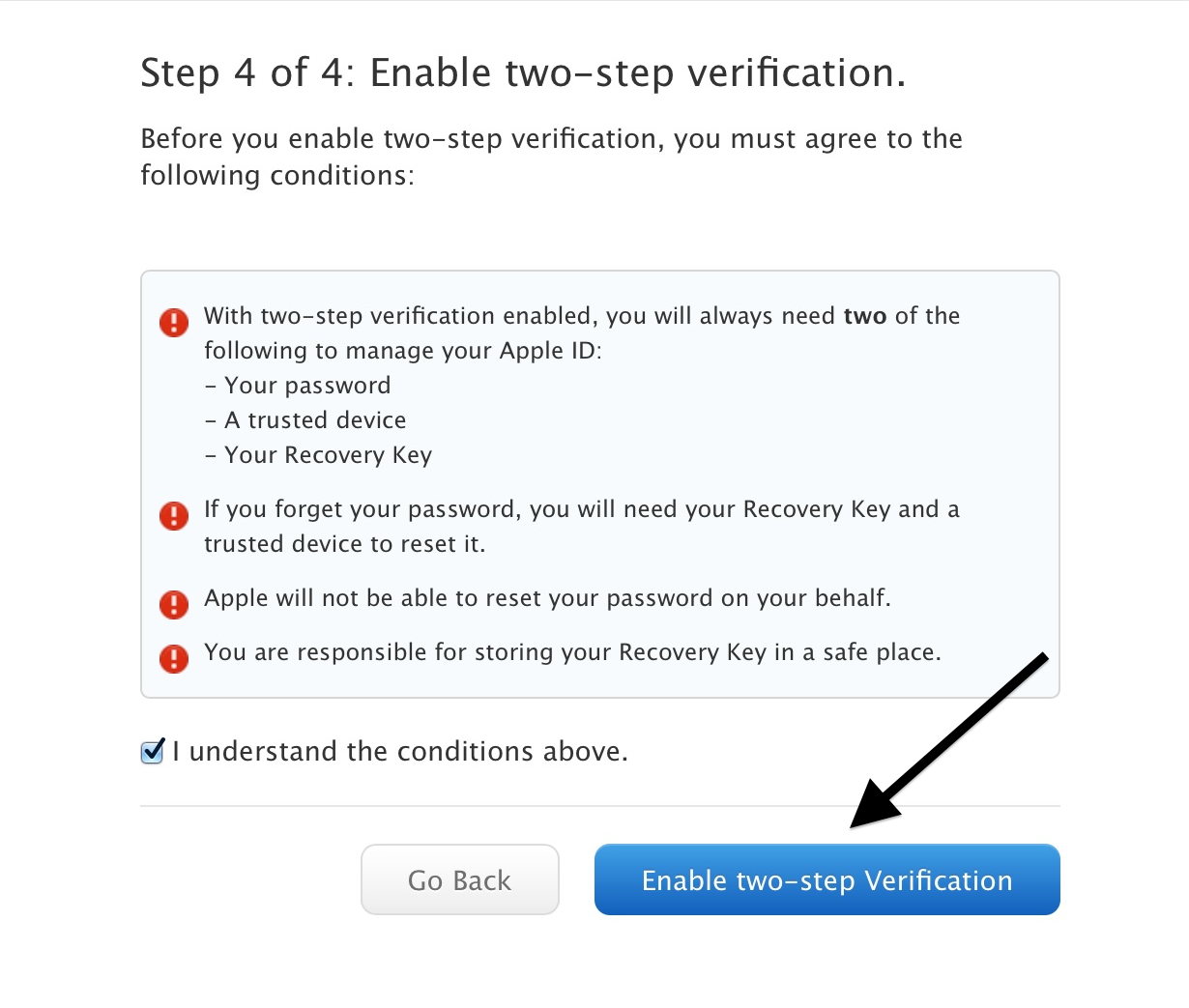
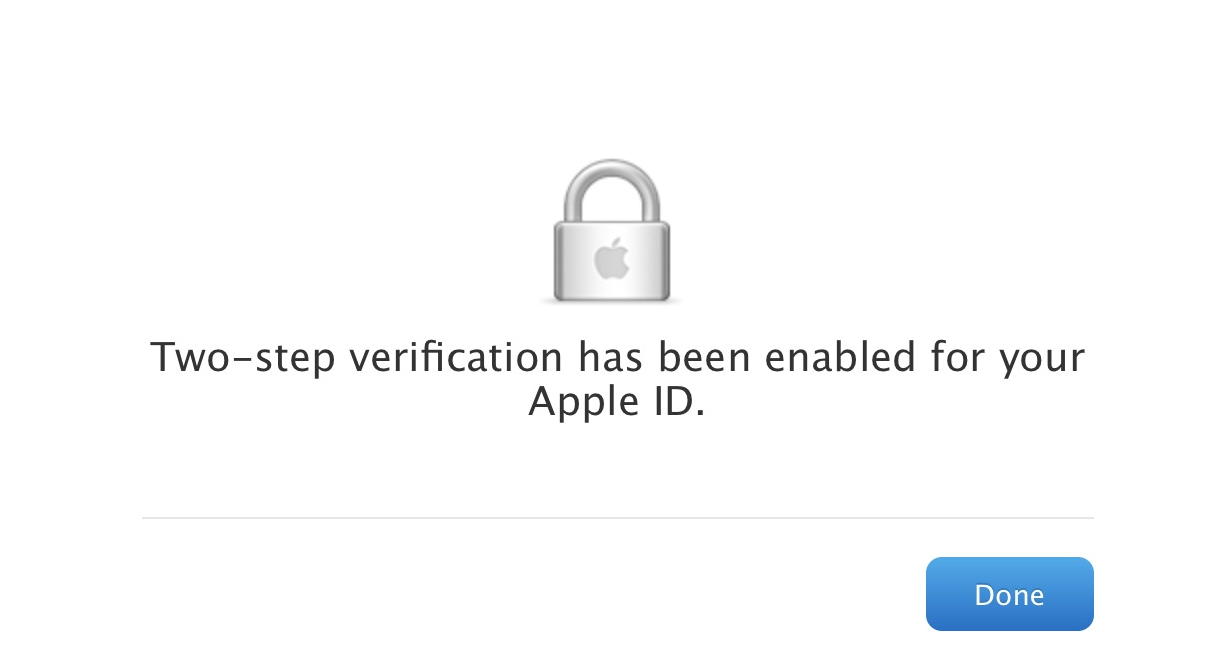
7. You’re almost there! Read the conditions presented to you and click the “I understand the conditions above.” checkbox.
Then take a deep breath and click “Enable two-step Verification”
Congratulations! You’ve now enabled Two-Factor Authentication on your Apple ID account. Logout and log back in to try it out.
DropBox
DropBox allows you to setup 2FA using SMS or a mobile application. For the purposes of this guide we’ll step through setting up 2FA using SMS only to be compatible with the most configurations of mobile phones.
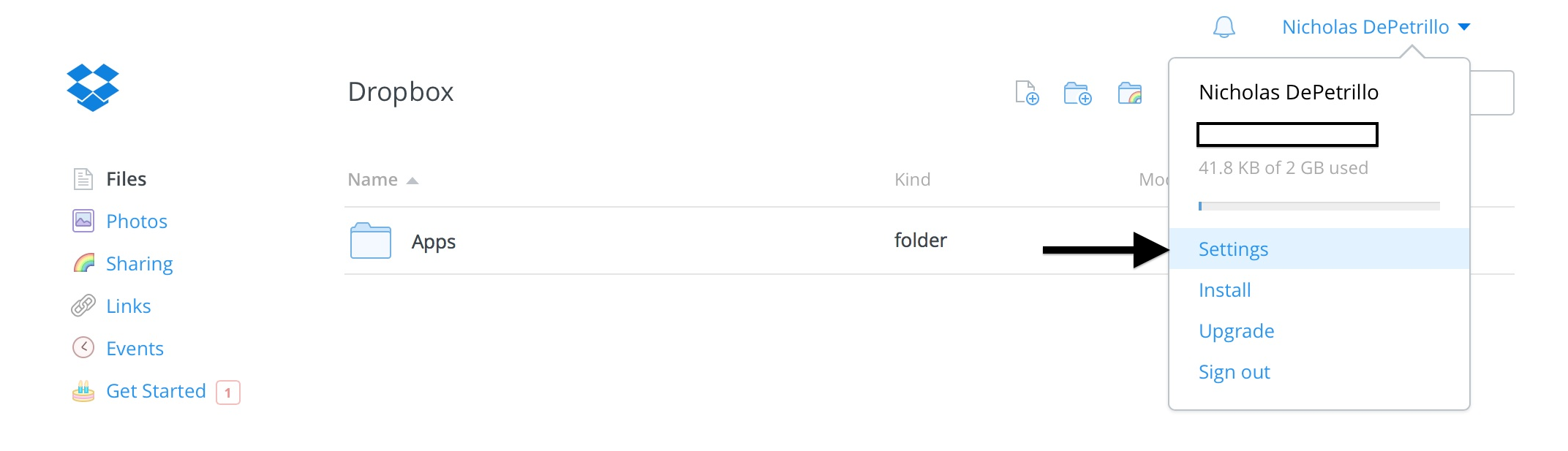
1. Login to your DropBox account and click your name in the top righthand corner of the screen. Select “Settings” from the drop down menu.
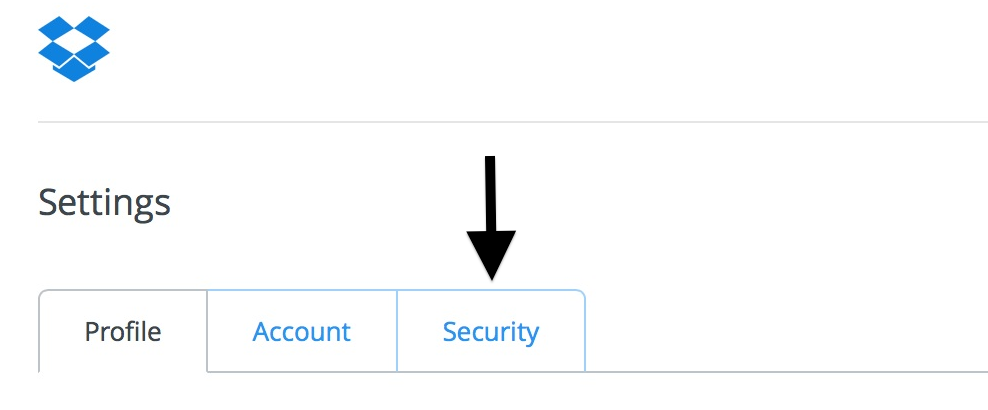
2. Click the “Security” tab in the top left hand portion of the page.
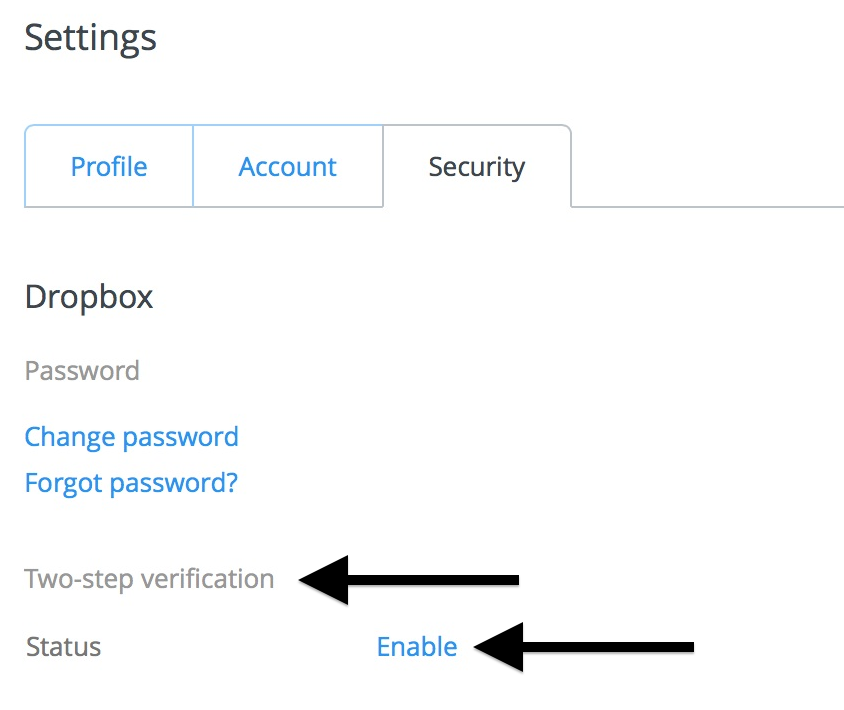
3. Under “Two-Step verification” click “Enable”
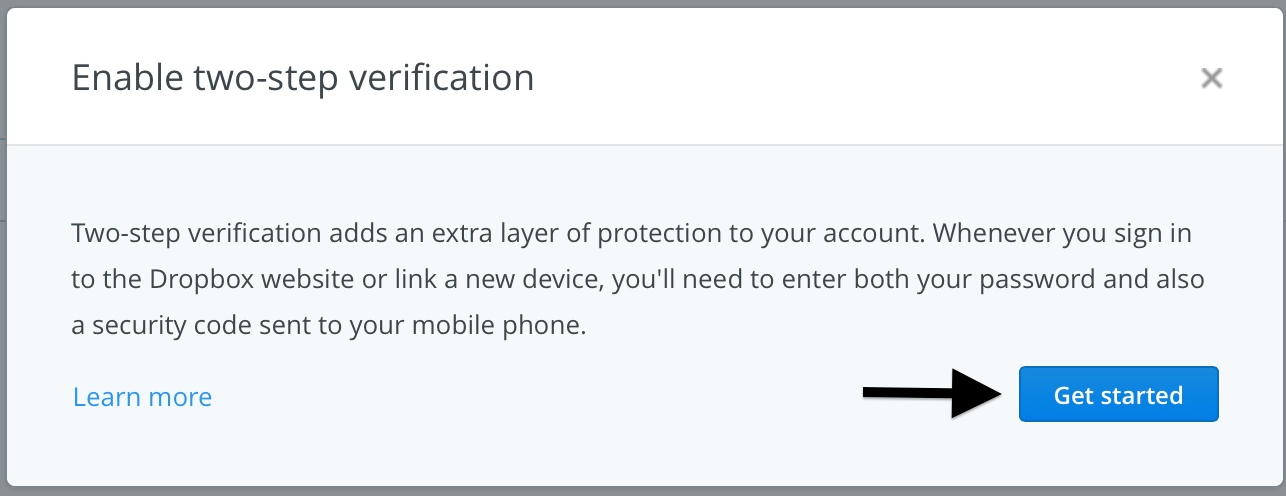
4. DropBox will display some information about their two-step verification process. Click “Get Started” to continue.
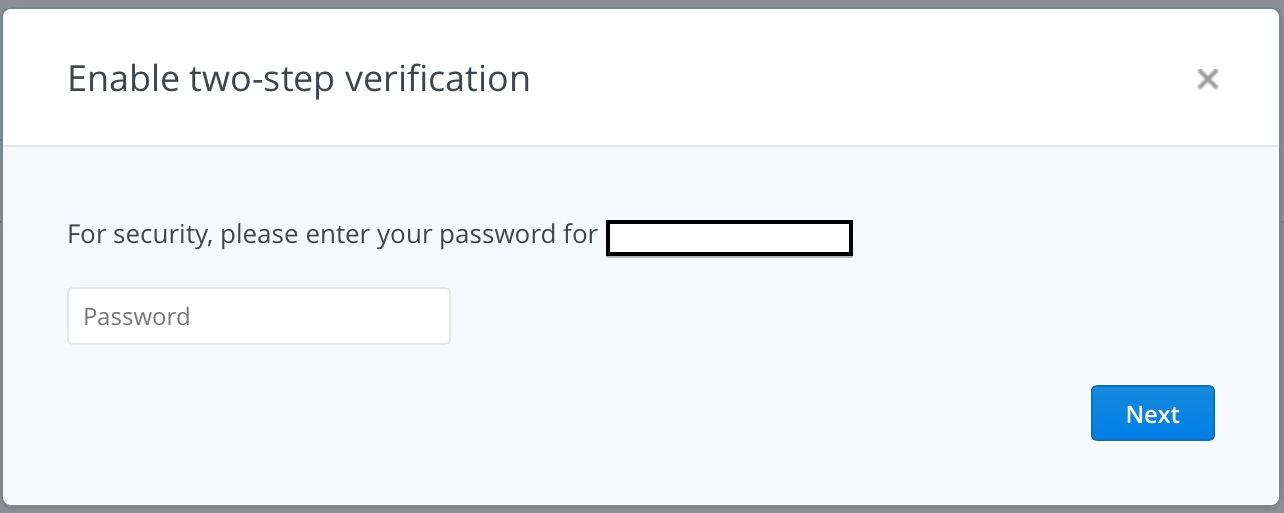
5. DropBox will ask you to enter your password to continue the two-step verification process.
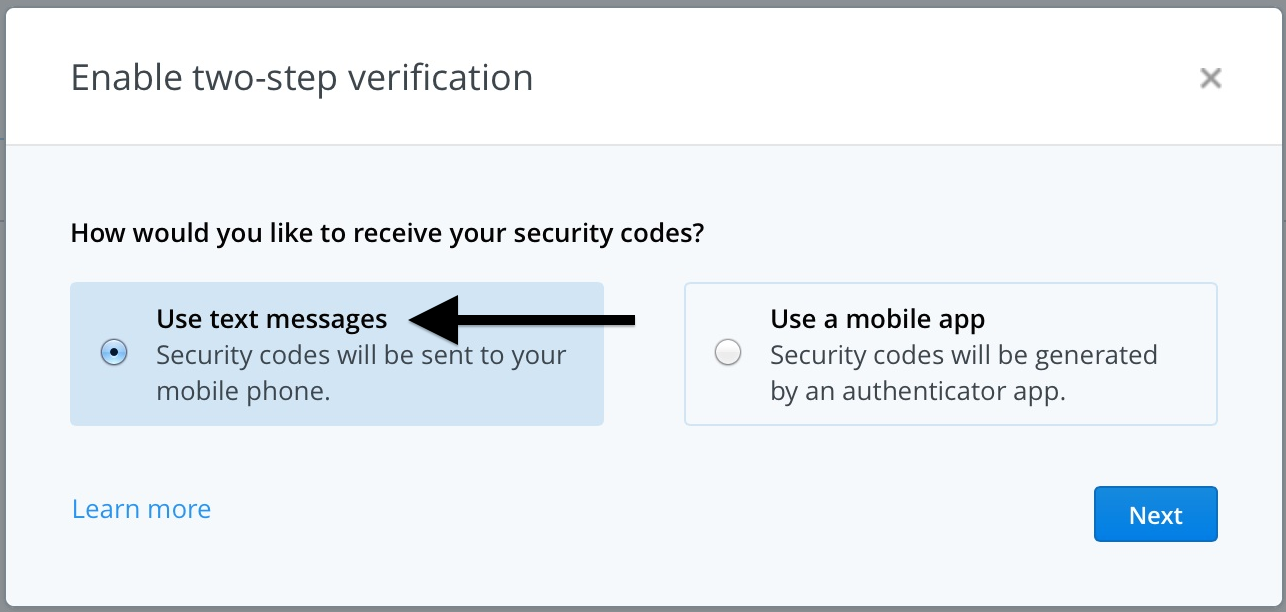
6. For the purposes of this tutorial we’ll select the “Use text messages” option. This will send 2FA codes to your phone as an SMS.
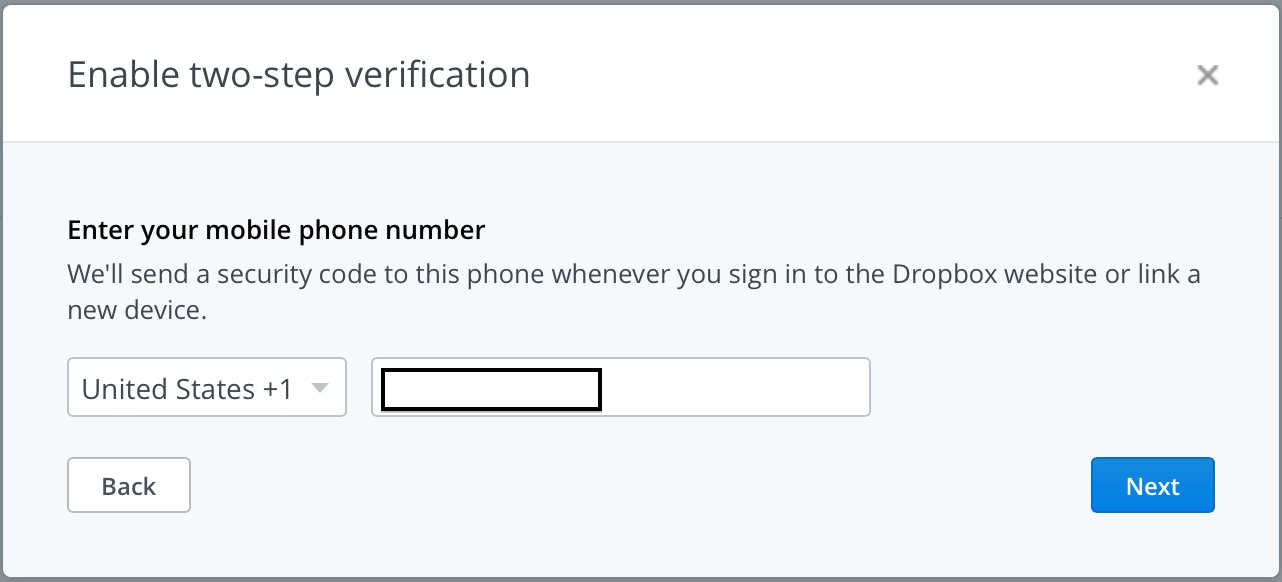
7. DropBox will ask for your mobile phone number.
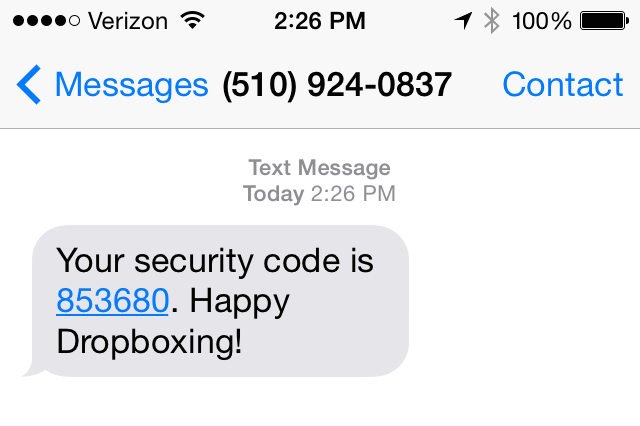
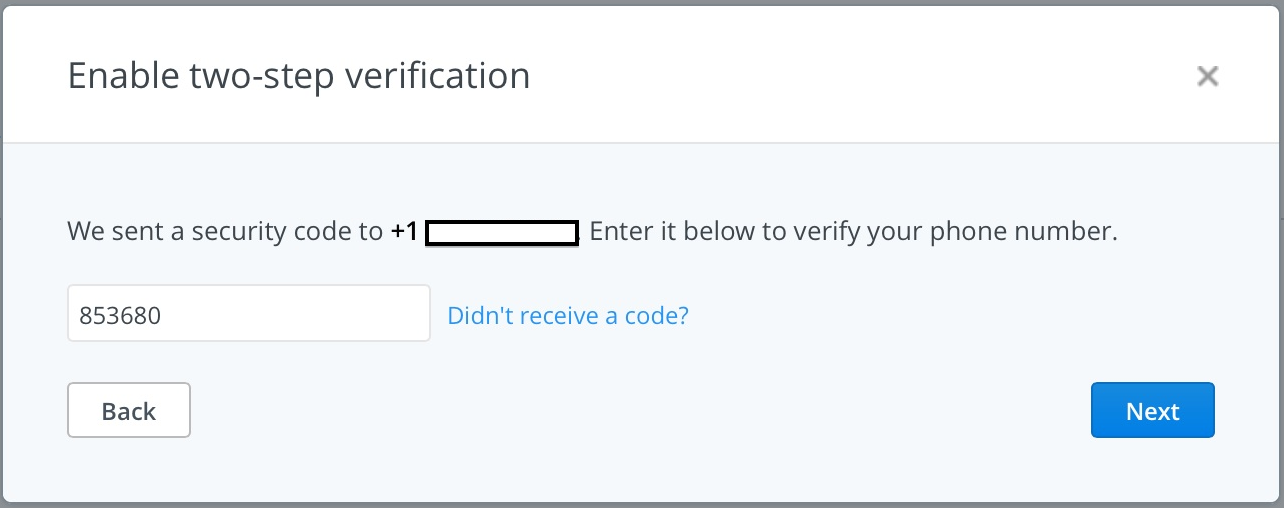
After your click “Next” an SMS will be sent to your phone with a “security code”.
DropBox will ask for the code and verify your phone number.
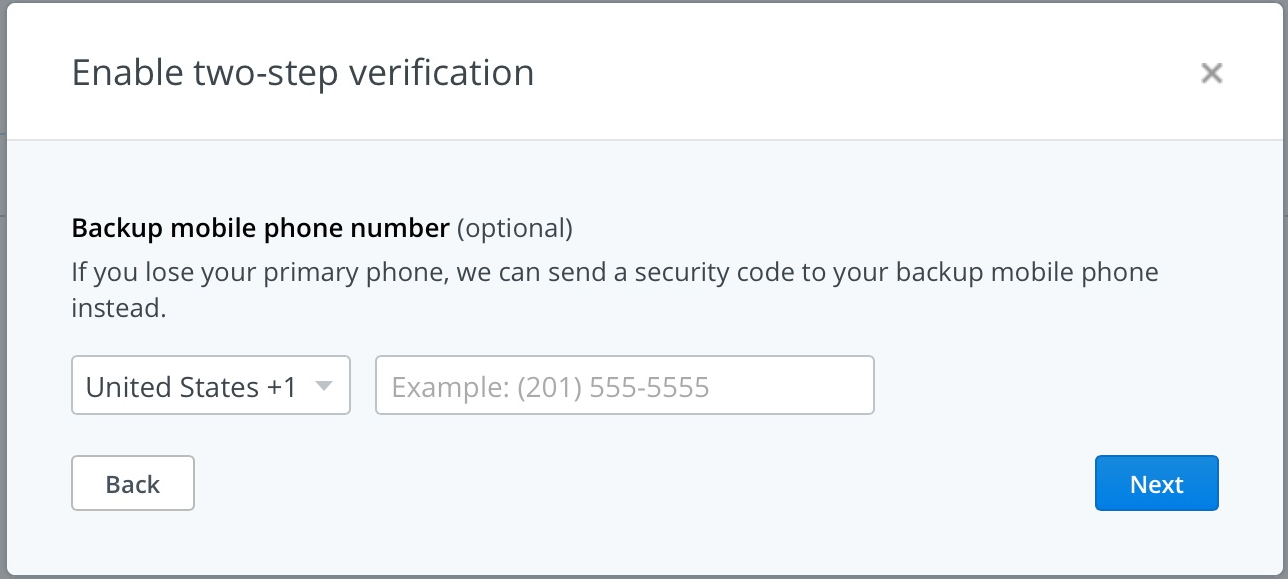
8. DropBox will ask if you wish to provide a backup mobile phone number. This is an optional step, if you choose to provide a backup number you will be required to repeat the process above for enrolling another mobile phone number.
9. Similar to Apple ID, DropBox will provide you with a “recovery key” or as they call it an “emergency backup code” to disable two-step verification in the event you lose possession of your phone or lose control of your mobile phone number.
Write it down and keep it safe, DropBox does not ask you to re-enter this code so make sure you keep a copy of it somewhere.
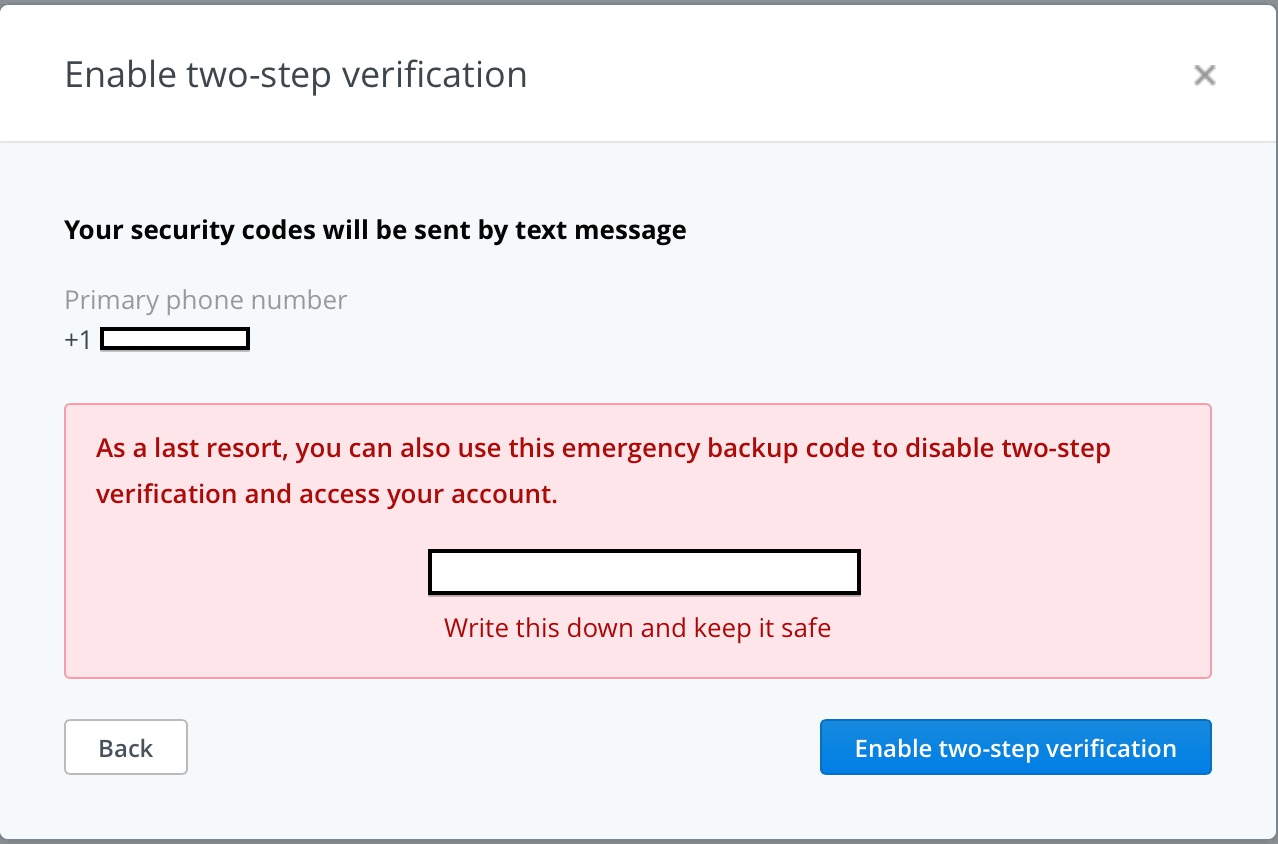
10. Finally, click “Enable two-step verification” and you’re finished!
Other Services
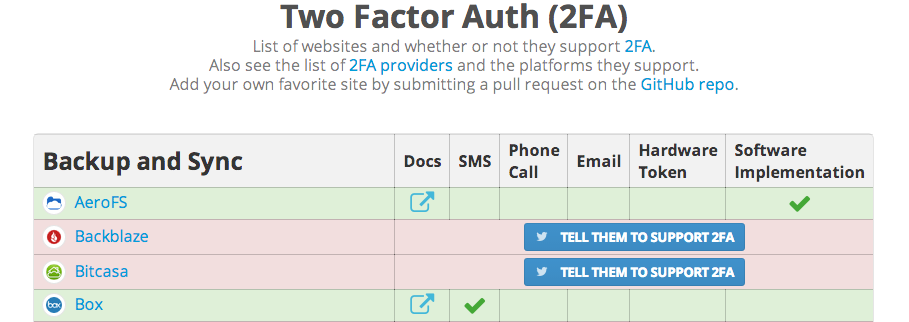
Many services other than Google, Apple and DropBox provide some form of 2FA. You may have to search around your account settings to locate the option to enroll. Not all services allow 2FA over SMS and may require the use of a mobile phone app such as Duo, Authy or another 2FA software vendor. Use twofactorauth.org to discover which services you use support 2FA:
Conclusion
Unfortunately, on today’s Internet you are responsible for your own security, even if you use web services from respectable Internet companies. Two-factor authentication significantly increases the security of your accounts by making stolen passwords harder to abuse. Enabling two-factor authentication is not without extra responsibility. You must be sure to setup 2FA on devices you control and protect any “recovery keys” in case you lose control of your device or mobile phone number. 2FA is not foolproof, but using it where you can will put you a head above the rest.
Update – Sep 16th, 2014
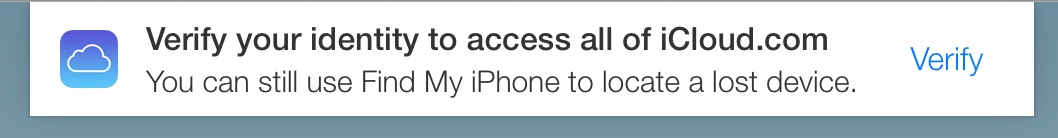
Apple has finally enabled two-factor authentication on iCloud.com. It now asks you to verify yourself via the 2FA method you signed up for using the above instructions.
Testing this with Elcomsoft’s iCloud forensics tool shows that 2FA is preventing the tool from logging in successfully even with a valid password.
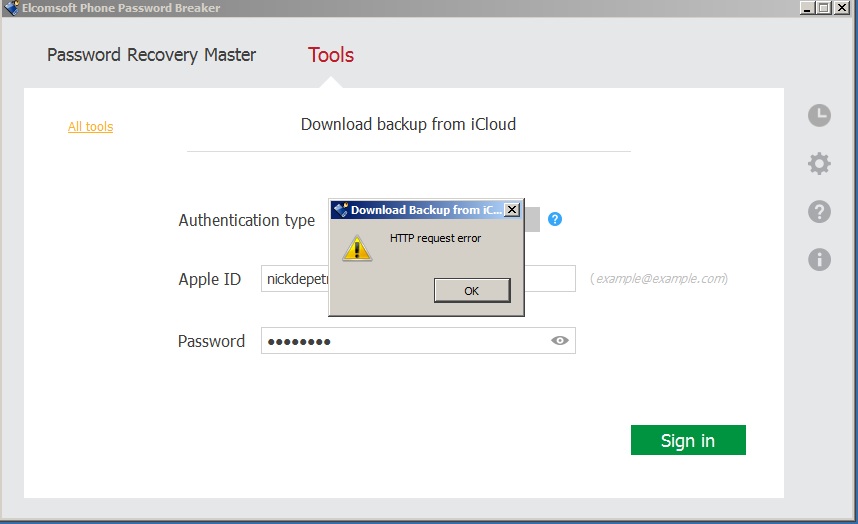 Elcomsoft may update the tool to support 2FA tokens, however it would still require an attacker to obtain access to the device or method in which you receive your 2FA tokens and utilize them before they expire. This is still much better than simply requiring just your username and password. It is raising the bar for the attacker to compromise your account.
Elcomsoft may update the tool to support 2FA tokens, however it would still require an attacker to obtain access to the device or method in which you receive your 2FA tokens and utilize them before they expire. This is still much better than simply requiring just your username and password. It is raising the bar for the attacker to compromise your account.